Logging
In the EasyLife application, efficient logging mechanisms are crucial for tracking activities and ensuring compliance. Here, we detail two primary logging methods integral to EasyLife's functionality.
Microsoft 365 Audit Logs
Microsoft 365 Audit Logs serve as a robust tool for comprehensively tracking app and user activities within EasyLife. By leveraging tailored filters for EasyLife 365 apps, customers can effortlessly navigate and review logged activities within their audit logs.
It's important to note that while audit logging is enabled by default for Microsoft 365 organizations, it's advisable to verify the auditing status when setting up a new Microsoft 365 organization. Learn more about audit logs here.
Event Logging
Event logging is another vital component, providing a structured approach to capturing governance activities within our applications. These activities are meticulously recorded in an analytics workspace of your choice, ensuring systematic documentation for future reference and compliance purposes.
By default, event logging is disabled. To enable it, navigate to the Logging tab and check the Log events box. Learn more about configuring event logging here.
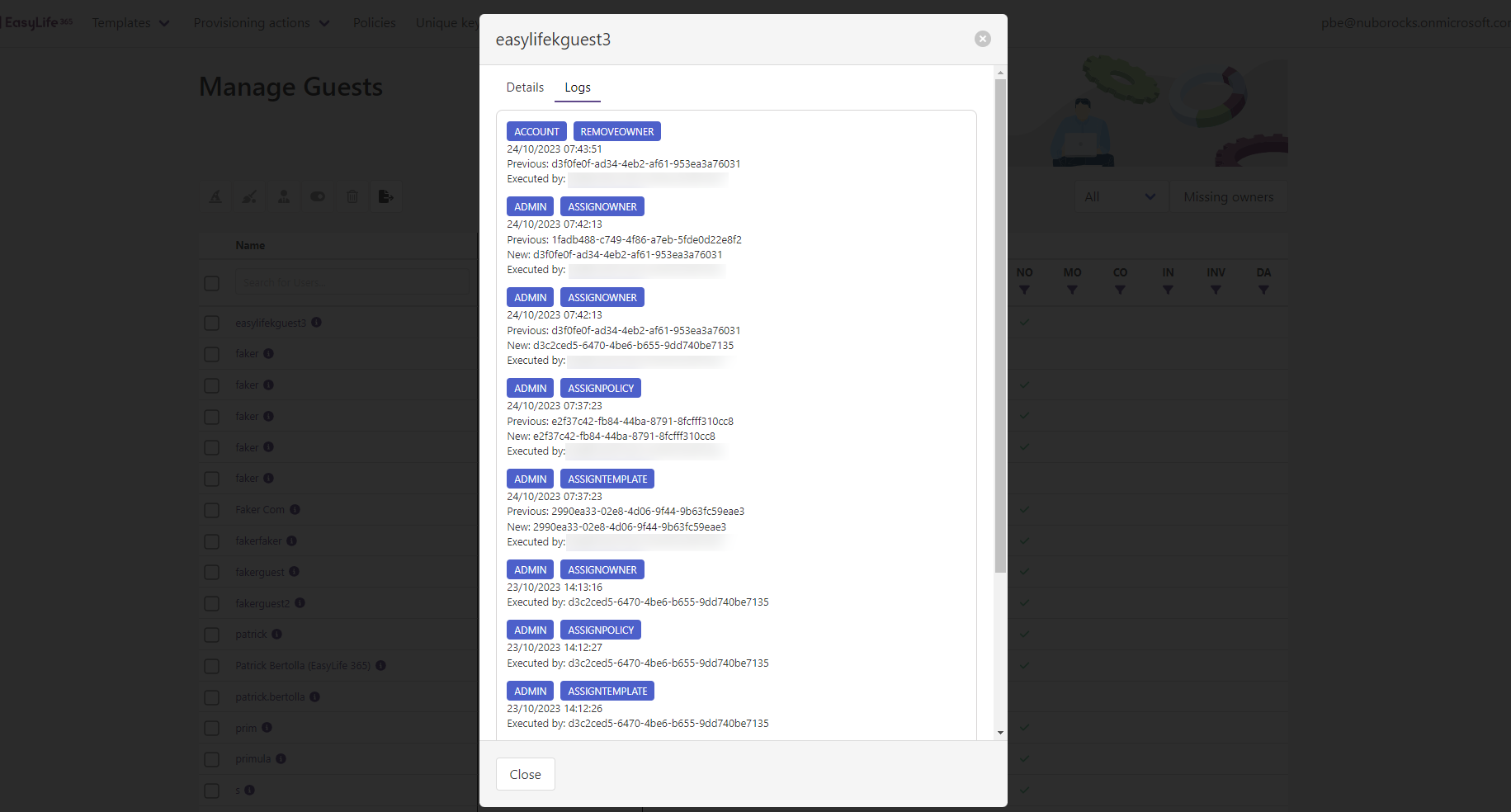
Viewing Resource Logs
To view logs of resources, ensure correct configuration of event logging in Read Mode.
Once event logging is enabled, governance events are seamlessly forwarded to your configured Application Insight. With data retention in your environment and read mode enabled, you can effortlessly monitor activities performed for a resource within the EasyLife 365 Cockpit. Follow these steps:
- Visit the manage section for the resource and click on the info button near the resource name.
- Click on the Logs tab to view all actions taken on this resource.
All event logs are neatly organized chronologically, with the newest entries appearing first.
Available Events
The following section outlines all events tracked through the event logging feature, categorized for clarity.
Guest Account Management
Admin Activities
| Category | EventId | Description |
|---|---|---|
| ADMIN | ASSIGN-POLICY | Assigns a policy to the resource |
| ADMIN | REMOVE-POLICY | Removes a policy from the resource |
| ADMIN | ASSIGN-TEMPLATE | Assigns a template to the resource |
| ADMIN | REMOVE-TEMPLATE | Removes a template from the resource |
| ADMIN | ASSIGN-OWNER | Assigns an owner to the guest account |
| ADMIN | REMOVE-OWNER | Removes an owner from the guest account |
| ADMIN | DELETE | Deletes a guest account |
User Activities
| Category | EventId | Description |
|---|---|---|
| ENGINE | INVITE | Engine invites a guest on behalf of another user |
| POLICY | SEND-INVITATION | Resends an invitation |
| ACCOUNT | DISABLE | Disables a guest |
| ACCOUNT | ENABLE | Enables a guest |
| ACCOUNT | DELETE | Deletes a guest |
| ACCOUNT | REMOVE-OWNER | An owner removes another owner from a guest |
| ACCOUNT | CHANGE-OWNER | Changes the owner for a guest |
| ACCOUNT | TAKE-OWNERSHIP | A user takes over the ownership of a guest |
| ACCOUNT | UPDATE-METADATA | Updates the metadata of a guest |
| POLICY | EXTEND-DISABLEMENT | Extends a disabled guest |
| POLICY | CONFIRM | Confirms a guest |
| POLICY | EXTEND-INACTIVITY | Extends an inactive guest |
Engine Activities
| Category | EventId | Description |
|---|---|---|
| ENGINE | DELETE | Deletes a guest due to an escalation |
| ENGINE | DISABLE | Disables a guest due to an escalation |
SharePoint Management
Admin Activities
| Category | EventId | Description |
|---|---|---|
| ADMIN | ASSIGN-POLICY | An admin assigns a policy to a site |
| ADMIN | REMOVE-POLICY | An admin removes a policy from a site |
| ADMIN | ASSIGN-TEMPLATE | An admin assigns a template to a site |
| ADMIN | REMOVE-TEMPLATE | An admin removes a template from a site |
| ADMIN | ASSIGN-OWNER | An admin assigns an owner to a site |
| ADMIN | REMOVE-OWNER | An admin removes an owner from a site |
| ADMIN | UNLINK-SITE | Unlinks the SharePoint site and deletes the associated security group |
| ADMIN | LINK-SITE | The admin converts a site to an EasyLife managed site and associates a security group |
User Activities
| Category | EventId | Description |
|---|---|---|
| POLICY | MINIMUMOWNER-COMPLIANT | An owner makes the minimum owner policy compliant |
| POLICY | MINIMUMOWNER-INCOMPLIANT | An owner makes the minimum owner policy incompliant |
| POLICY | ASSIGN-TEMPLATE | An owner assigns a template to a site |
| POLICY | EXTEND-EXPIRATION | An owner makes an expired site compliant |
| POLICY | ASSIGN-POLICY | An owner assigns a policy to a site |
| POLICY | CONFIRM | An owner confirms a site |
| POLICY | COMPLETE-ACESSREVIEW | An owner completes an access review |
| ACCOUNT | DELETE | An owner deletes a SharePoint site with EasyLife |
Engine Activities
| Category | EventId | Description |
|---|---|---|
| ENGINE | ASSOCIATE-GROUP-TO-SITE | The EasyLife Security Group is associated with the site |
| ENGINE | SYNC-SITE | Permission synchronization is performed between the associated group and site admins |
| ENGINE | DELETE | A site is deleted by EasyLife |
| ENGINE | DELETE-SPO-GROUP | The SharePoint Security Group was deleted permanently after 90 days |
Groups Management
Admin Activities
| Category | EventId | Description |
|---|---|---|
| ADMIN | ASSIGN-POLICY | An admin assigns a policy to a group |
| ADMIN | REMOVE-POLICY | An admin removes a policy from a group |
| ADMIN | ASSIGN-TEMPLATE | An admin assigns a template to a group |
| ADMIN | REMOVE-TEMPLATE | An admin removes a template from a group |
| ADMIN | ASSIG-NOWNER | An admin assigns an owner to a group |
| ADMIN | REMOVE-OWNER | An admin removes an owner from a group |
| ADMIN | DELETE | An admin deletes a group |
User Activities
| Category | EventId | Description |
|---|---|---|
| ACCOUNT | DELETE | Deletes a group |
| ACCOUNT | ARCHIVE-TEAM | Archives a team with EasyLife |
| ACCOUNT | UNARCHIVE-TEAM | Unarchives a team with EasyLife |
| ACCOUNT | START-ACCESSREVIEW | Starts an access review |
| ACCOUNT | CANCEL-ACCESSREVIEW | Cancells an access review |
| ACCOUNT | COMPLETE-ACCESSREVIEW-STEP | Completes an access review step |
| ACCOUNT | TAKE-TEAM-CHANNEL-OWNERSHIP | Takes over a channel ownership if there are no other owners assigned during an access review |
| ACCOUNT | GET-ACCESSSREVIEW | Retrieves the access review |
| ACCOUNT | COMPLETE-ACCESSREVIEW | Completes the access review |
| POLICY | CONFIRM | Confirms a group |
| POLICY | EXTEND-EXPIRATION | Extends a group that is not in use |
| POLICY | ASSIGN-TEMPLATE | Assigns a target template using a template policy |
| POLICY | ASSIGN-POLICY | Assigns a target policy using a template policy |
| POLICY | MINIMUMOWNER-COMPLIANT | An owner makes the minimum owner policy compliant |
| POLICY | MINIMUMOWNER-INCOMPLIANT | An owner makes the minimum owner policy incompliant |
Engine Activities
| Category | EventId | Description |
|---|---|---|
| ENGINE | CREATE-GROUP | Creates a group on behalf of a user |
| ENGINE | CREATE-TEAM | Creates a team on behalf of a user |
| ENGINE | ARCHIVE-TEAM | Archives a team due to an escalation |
| ENGINE | DELETE | Deletes a group due to an escalation |
| ENGINE | REMOVE-GUESTS | Deletes guests from a group due to an escalation |
| ENGINE | REMOVE-MEMBERS-AND-GUESTS | Removes members and groups due to an escalation |
Collected Values
Each event entry contains essential details including ObjectId, DisplayName, Category, EventId, PreviousValue, NextValue, Description, CreatedBy, and Created.
Querying Event Logs
Upon successful connection of your Application Insights and Log Analytics Workspace, you can execute queries on the log analytics workspace to retrieve log information. Below are examples of such queries:
- Retrieve all logs in chronological order:
AppTraces
| project
EventId = Properties.eventId,
Category = Properties.category,
ResourceId = Properties.resourceId,
Name = Properties.name,
Description = Properties.description,
Actor = Properties.actor,
PreviousValue = Properties.previousValue,
NextValue = Properties.nextValue,
TimeGenerated
| order by TimeGenerated desc
- Retrieve all events that executed a deletion operation
AppTraces
| project
EventId = Properties.eventId,
Category = Properties.category,
ResourceId = Properties.resourceId,
Name = Properties.name,
Description = Properties.description,
Actor = Properties.actor,
PreviousValue = Properties.previousValue,
NextValue = Properties.nextValue,
TimeGenerated
| where EventId == 'DELETE'
| order by TimeGenerated desc